Monday, May 22, 2024
Verifiable Data Mistakes That Undermine Compliance Claims
by
Published
Views:
Across modern manufacturing, compliance claims can collapse when verifiable data is incomplete, outdated, or poorly documented. From vehicle technology and manufacturing tools to industrial filtration, CO2 removal, and sustainable water solutions, weak evidence undermines manufacturing standards, procurement insights, and manufacturing efficiency. This article examines the most common data mistakes that damage credibility and the digital foundations needed to support defensible compliance.
For most buyers, engineers, quality teams, and project leaders, the core issue is not whether a supplier says a product is compliant. It is whether that claim can withstand audit, technical review, customer challenge, and operational use. In practice, compliance failures often begin with small but verifiable data mistakes: a test report tied to the wrong revision, a certificate with no traceable scope, outdated material declarations, or performance data presented without the conditions needed to validate it. These gaps create procurement risk, delay approvals, weaken quality assurance, and can expose organizations to legal and commercial consequences.
If your role involves technical evaluation, sourcing, compliance review, or implementation, the most useful question is simple: Can this claim be proven consistently, with current, traceable, and context-rich data? That is the standard that separates defensible compliance from marketing language.
Which Verifiable Data Mistakes Most Often Break Compliance Claims?

The most damaging mistakes are usually not dramatic fraud cases. They are ordinary documentation and data-governance failures that make a claim impossible to verify. Across electronics, automotive systems, water infrastructure, agri-tech equipment, and industrial tooling, several patterns appear repeatedly.
1. Using outdated certificates, reports, or declarations
A common failure is relying on an expired test report, obsolete standard version, or old supplier declaration. A component may once have met the requirement, but if the evidence no longer reflects the current product revision, process configuration, or regulatory framework, the claim becomes weak. This is especially risky when procurement teams reuse legacy files from previous sourcing rounds without checking validity dates, standard updates, or engineering changes.
2. Missing traceability between product, batch, and evidence
A compliance claim is only as strong as its link to the exact item being supplied. If a report names a model family but not the precise configuration, lot, material code, firmware version, or manufacturing site, quality and safety teams cannot confirm that the shipped product matches the tested product. In high-mix industrial environments, this traceability gap is one of the fastest ways to undermine technical credibility.
3. Test data without conditions, methods, or scope
Performance and compliance results often look convincing until someone asks: under what test method, operating condition, environmental setting, load profile, or acceptance criteria? A filtration module efficiency number, EV subsystem durability result, or substrate reliability claim means little if the test setup is missing. Without context, procurement and engineering teams cannot compare suppliers fairly or determine real-world applicability.
4. Inconsistent data across departments and documents
One document states one material composition, another lists a different supplier, and a third references a different revision level. These inconsistencies often appear when sales, engineering, compliance, and operations maintain separate records. Even if each file looks reasonable by itself, conflicts across the dataset make the overall compliance claim unreliable.
5. Unsupported self-declarations
Self-declarations are not automatically invalid, but they are frequently overused. If a supplier claims conformity without accredited testing, recognized standard references, auditable quality controls, or documented technical rationale, the burden of verification shifts to the buyer. For regulated or quality-critical applications, that is rarely acceptable.
6. Poor change-control documentation
Products evolve. Materials change, software updates are released, second-source components are introduced, and process settings are optimized. If the organization cannot show what changed, when it changed, who approved it, and whether compliance was reassessed, previously valid claims may no longer be defensible.
Why These Data Errors Matter to Procurement, Engineering, and Quality Teams
These mistakes do more than create paperwork problems. They directly affect business decisions, project timing, and operational risk.
For procurement teams, weak verifiable data increases supplier-selection risk. Buyers may approve a source based on attractive specifications, only to face onboarding delays, customer rejection, or non-conformance costs later. This can disrupt sourcing strategy and damage total cost performance.
For technical evaluators and engineers, incomplete evidence makes benchmarking impossible. If a motor, PCB substrate, membrane system, or precision tool cannot be tied to robust test data and standard references, engineers cannot judge fitness for use or compare alternatives with confidence.
For quality and safety managers, weak evidence creates audit exposure. During internal review, customer qualification, or third-party assessment, undocumented gaps can trigger corrective actions, shipment holds, or escalation.
For project managers and commercial decision-makers, the problem is timing. Compliance uncertainty appears late in many projects, often after design freeze, supplier nomination, or installation planning. At that stage, even small documentation failures can delay milestones and inflate costs.
In short, verifiable data is not an administrative extra. It is part of the operational foundation for manufacturing efficiency, risk mitigation, and defensible market claims.
How to Tell Whether a Compliance Claim Is Actually Defensible
Readers in industrial sectors usually do not need more theory. They need a practical screening framework. A defensible compliance claim should meet five tests.
Identity test: Does the evidence clearly match the product?
Check part number, revision, configuration, software or firmware version, manufacturing site, and if relevant, batch or lot traceability. If the evidence cannot be tied to the specific deliverable, treat the claim as incomplete.
Validity test: Is the evidence current?
Review issue dates, expiry dates, standard versions, and engineering change history. A valid document from three years ago may no longer be valid for the current design or applicable requirement.
Method test: Is the verification approach transparent?
Look for cited standards, test methods, sample conditions, acceptance thresholds, and laboratory or inspection scope. If the method is unclear, the result is difficult to trust and impossible to benchmark properly.
Consistency test: Do all documents tell the same story?
Compare declarations, drawings, specifications, quality records, inspection results, and marketing claims. Misalignment is often the first visible sign of deeper compliance-control issues.
Governance test: Is there a documented process for updates and exceptions?
Even strong evidence loses value if there is no system for maintaining it. Ask how changes are reviewed, who owns the data, how revalidation is triggered, and how obsolete records are retired.
If a supplier or internal team cannot answer these five questions cleanly, the compliance claim may not survive audit or field scrutiny.
What Strong Digital Foundations Look Like in Practice
Because compliance evidence spans multiple teams, the underlying problem is often not lack of effort but fragmented data architecture. Strong digital foundations reduce this problem by making technical, quality, and sourcing information easier to verify and maintain.
Centralized source of truth
Critical compliance records should not be scattered across inboxes, local folders, and disconnected spreadsheets. A centralized system should connect specifications, test reports, declarations, supplier records, and revision histories in a controlled environment.
Version control and document lineage
Users must be able to see which document is current, what changed, and what it replaced. This is essential for standards-based industries where even minor design updates can affect conformity.
Linked technical and commercial data
Compliance review is stronger when procurement data, approved vendor information, part master data, and technical validation records are connected. This reduces the risk of buying a variant that differs from the one originally assessed.
Structured metadata for search and audit
Documents become more useful when tagged by product family, standard, region, revision, material class, production site, and validity period. This allows quality, sourcing, and engineering teams to retrieve evidence quickly during evaluations or audits.
Automated alerts for expiry, change, and requalification
Many compliance failures happen because no one notices that a report has expired or a material has changed. Automated monitoring helps teams act before a compliance gap becomes a delivery issue.
For organizations operating across sectors such as automotive, electronics, smart agriculture, and environmental infrastructure, these digital foundations are especially important because standards, supplier networks, and qualification requirements overlap but are not identical.
What Buyers and Technical Teams Should Ask Before Accepting a Claim
To reduce ambiguity, decision-makers should ask focused questions early. The goal is not to create bureaucracy, but to expose whether the supplier or internal owner can support the claim with verifiable data.
- What exact standard or requirement is this claim referencing?
- Which product revision and configuration does the evidence cover?
- Who performed the test, inspection, or certification, and under what scope?
- What operating conditions or assumptions apply to the reported result?
- Has anything changed in materials, process, software, or source location since validation?
- How is document validity monitored and updated?
- Can the claim be traced from marketing statement to technical file to delivered product?
These questions are useful for procurement qualification, supplier audits, pre-award reviews, engineering approvals, and distributor due diligence. They also help non-specialist commercial stakeholders distinguish between a polished presentation and a robust compliance position.
How Better Data Improves Trust, Speed, and Manufacturing Efficiency
When compliance data is current, traceable, and structured, the benefits extend beyond risk reduction.
Supplier onboarding becomes faster because technical and quality reviewers can approve evidence without repeated clarification cycles. Cross-functional alignment improves because procurement, engineering, and quality teams work from the same verified record set. Customer trust increases because claims can be defended with documentation rather than explanation alone. Most importantly, manufacturing efficiency improves when fewer projects are delayed by late-stage compliance uncertainty.
This is why verifiable data matters across the full industrial lifecycle. It supports better benchmarking, stronger procurement insights, more reliable quality decisions, and more resilient global supply chains.
Conclusion: Compliance Claims Fail Quietly Before They Fail Publicly
The biggest compliance risks are often visible long before any formal failure occurs. They appear as outdated files, broken traceability, inconsistent records, missing test context, and unmanaged change. For information researchers, operators, evaluators, buyers, quality managers, and project leaders, the practical takeaway is clear: do not judge compliance by the existence of documents alone. Judge it by whether the claim is supported by verifiable data that is current, traceable, consistent, and governed.
Organizations that build around this discipline are better positioned to compare suppliers accurately, defend technical claims confidently, and operate with higher resilience. In modern manufacturing, compliance credibility is no longer based on statements. It is built on evidence that can be verified end to end.
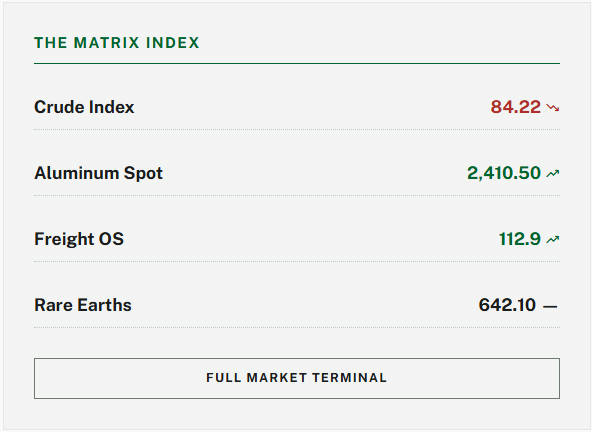
The Archive Newsletter
Critical industrial intelligence delivered every Tuesday. Peer-reviewed summaries of the week's most impactful logistics and market shifts.